Security System Maintenance Packages
Regular maintenance is essential to keep your security systems compliant, reliable and performing at their best. SecureSense provides structured, professional maintenance packages for Access Control, CCTV, and Intruder Alarm Systems, tailored for commercial and industrial environments.
Choose from Bronze, Silver or Gold depending on the level of support your site requires.
Maintenance & Support Plans
Protect your security investment with flexible maintenance options designed to maximise uptime, improve system reliability and provide rapid support when needed.
Gold Premium
Our highest level of cover for clients who require maximum uptime, predictable maintenance costs and priority service delivery.
Includes:
• 1 annual preventative maintenance visit
• Full technical support
• Reactive service labour included
• Replacement of faulty parts*
• Priority response times
• System performance review and lifecycle guidance
*Subject to agreed system scope, exclusions and manufacturer availability.
Silver Standard
A balanced maintenance solution providing priority support and reduced operational disruption while keeping ownership flexible.
Includes:
• Full technical support
• Reactive service labour included
• Preferential rates on non-warranty parts
• Priority response times
• Optional preventative maintenance visits
Bronze Basic
A flexible pay-as-you-go support option for organisations requiring access to engineering support without a maintenance agreement.
Includes:
• Access to technical support
• Chargeable reactive call-outs
• Standard labour and parts rates
• Best endeavours response service
• No annual maintenance commitment
WHAT’S INCLUDED IN EVERY PACKAGE
✔ Professional, clean, compliant maintenance
✔ Detailed reporting for your records
✔ Recommendations for upgrades & lifecycle planning
✔ Support from an engineer with 20+ years’ experience
✔ Clear communication & reliable service

OPTIONAL ADD‑ONS
Available for any package:
• Out‑of‑hours support
• Remote monitoring setup
• System lifecycle & obsolescence reporting
• System upgrade planning
• Additional maintenance visits
• Emergency callout cover
Need a Bespoke Maintenance Agreement?
No two sites operate the same way. Securesense can build a tailored maintenance and support agreement around your systems, operational requirements and business priorities.
Whether you require planned preventative maintenance, rapid fault response, lifecycle support or full managed service delivery, maintenance packages can be designed to match your environment and budget.
Bespoke Support Options Include:
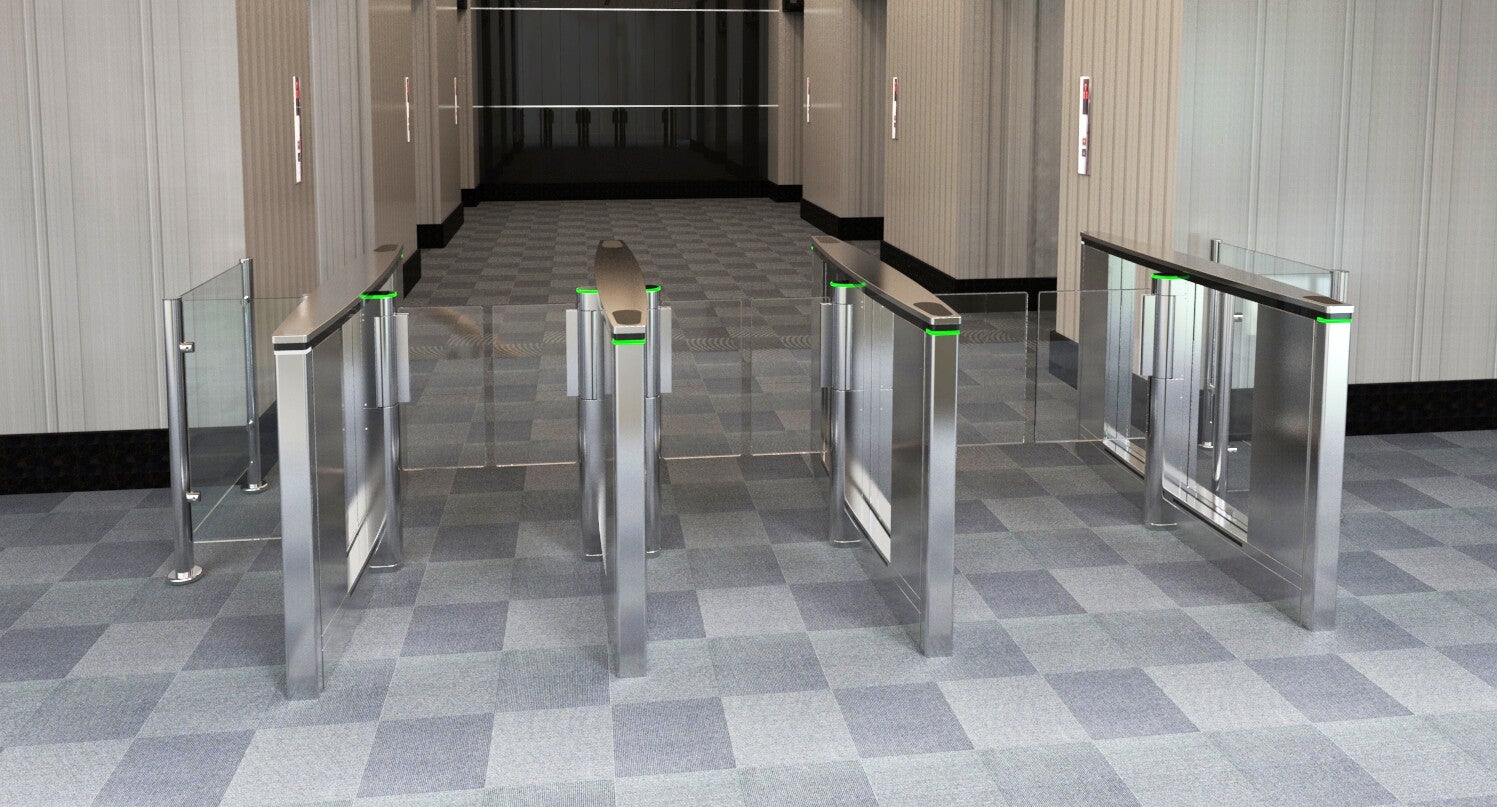
✓ Access Control Systems
✓ CCTV & Video Surveillance
✓ Intruder Alarm Systems
✓ Intercom & Entry Systems
✓ Integrated Security Platforms
✓ Multi-Site Maintenance Agreements
✓ Preventative Maintenance Programmes
✓ Reactive Fault Response
✓ Remote Technical Support
✓ Asset Lifecycle Planning & Reporting
✓ Out-of-Hours & Emergency Support
✓ Parts Inclusion Options
Ideal For:
• Commercial Buildings
• Offices & Corporate Environments
• Industrial & Manufacturing Sites
• Data Centres
• Multi-Site Estates
• Facilities Management Providers
• Property Management Companies
Tell us about your site and we’ll design a maintenance package that fits your operational requirements — not the other way around.
Choose the Right Maintenance Package for Your Business
Whether you need essential annual maintenance or full premium support, Securesense provides reliable, professional and technically sound security system care.

